Ho Chi Minh on 16/11… AUMI and PULS – A prestigious German brand in power supplies and the worldwide company focuses entirely on the development and production of DIN power supplies – organizes the conference revolves around the theme “Setting a new standard for power supply” on the 9th floor, Sacom – Chip Sang Building (SCS Building) Ho Chi Minh City.

The seminar had the participation of foreign experts from PULS: Mr. Lynus Heng – General Director of PULS, Mr. Yoshua Furutani – Director of Sales and Marketing, Mr. Eric Quek – Application Engineer and representatives of the department. leaders of Aumi company with the large participation of guests from companies and factories in Ho Chi Minh.
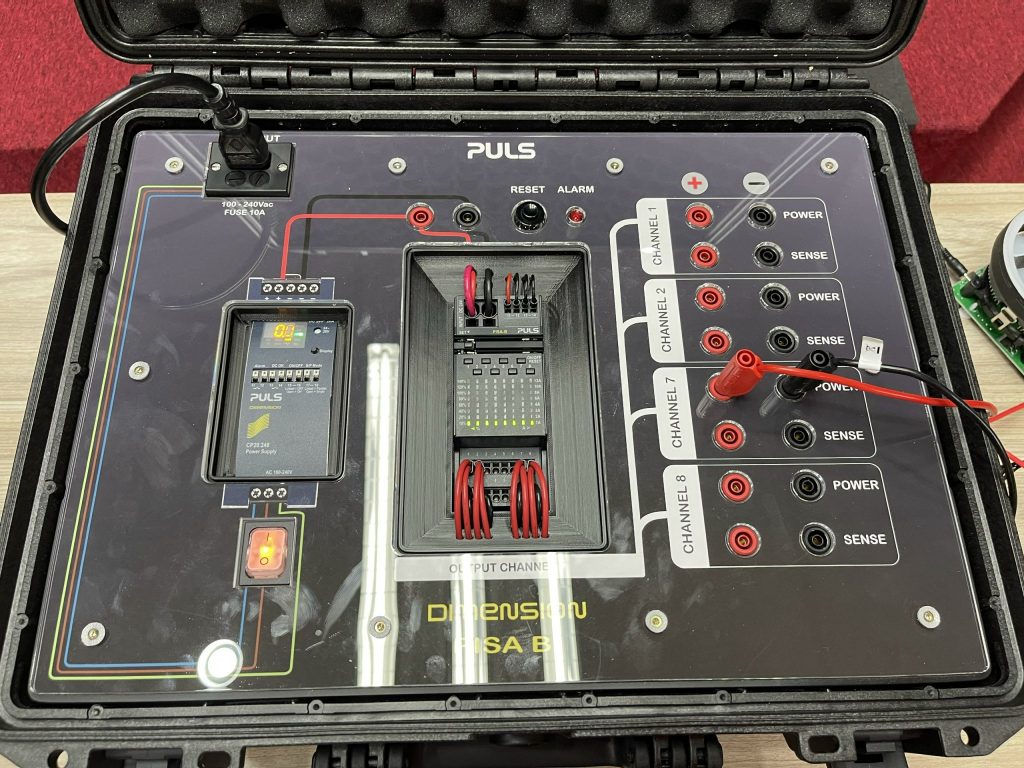
At the seminar, PULS experts shared about the importance of performance for power equipment, introduced and demoed live the application of PULS power product lines such as FIEPOS power supplies, Pisa modules.

The customers and Puls technical and product experts also discussed about the problems and solutions when using power supplies at their companies.
The PULS seminar with the theme “Setting a new standard for power supplies” brings a new perspective to businesses on using power supplies in production for factories and industrial parks. The seminar created an opportunity for AUMI to cooperate long-term with companies in the future, especially the opportunity to introduce, expand and develop the PULS product line in the Vietnamese market.




Website Editorial Board Aumi